📖 Topics Covered
Topic 1: Need of Blockchain
Once upon a time in a village named Techgaon, all the villagers used a big notebook in the town hall to record important things — who owned which land, who borrowed money from whom, and who had paid their taxes.
At first, this system worked well because everyone trusted the town clerk, Mr. Narayana, who managed the notebook.
But one day, Mr. Narayana made a mistake. Some people bribed him to change records in their favor. The villagers started arguing:
- "That land is mine!"
- "No, it says here I own it!"
- "But I never signed that!"
The village descended into chaos. That’s when a young girl named Sanika came forward with a revolutionary idea.
Sanika explained:
- Each person keeps a copy of the ledger.
- Every new transaction is checked by everyone.
- Once verified, the block is locked using a hash.
- Blocks are linked to form a chain.
🎯 Moral of the Story (Why We Need Blockchain)
- ✅ To remove the need for a middleman.
- ✅ To make records tamper-proof and transparent.
- ✅ To ensure trust through technology.
- ✅ To protect against fraud, hacking, and manipulation.
Topic 2: What is Blockchain?
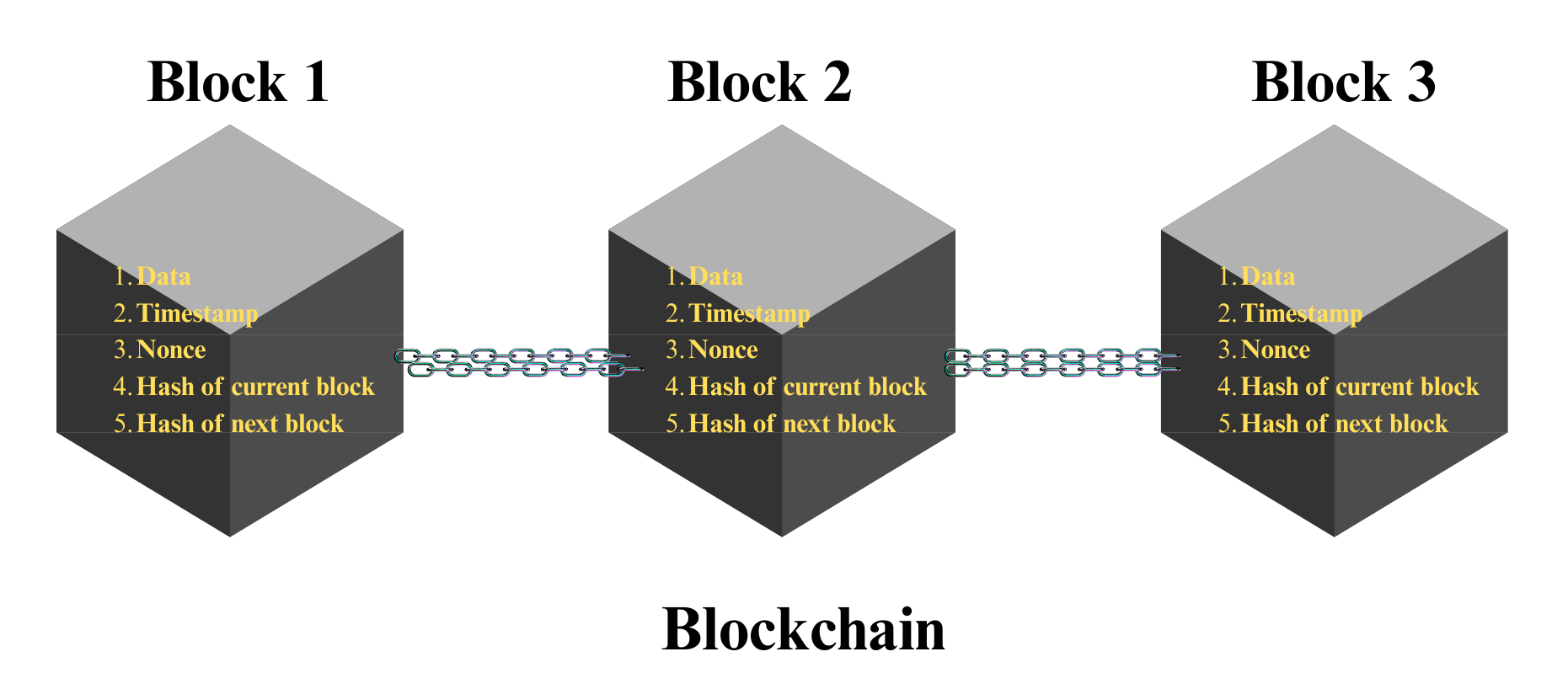
A blockchain is a sequence of blocks (like digital pages), where each block contains key components and is securely linked to the previous one.
📦 Internal Structure of Block:
1️⃣ Data
Stores information like financial transactions, smart contracts, etc.
2️⃣ Timestamp
Records exactly when the block was created.
3️⃣ Nonce ("Number Only Used Once")
The "magic number" used in mining to find a valid hash.
4️⃣ Hash of the Current Block
Unique fingerprint of the block content. Changes completely if data changes.
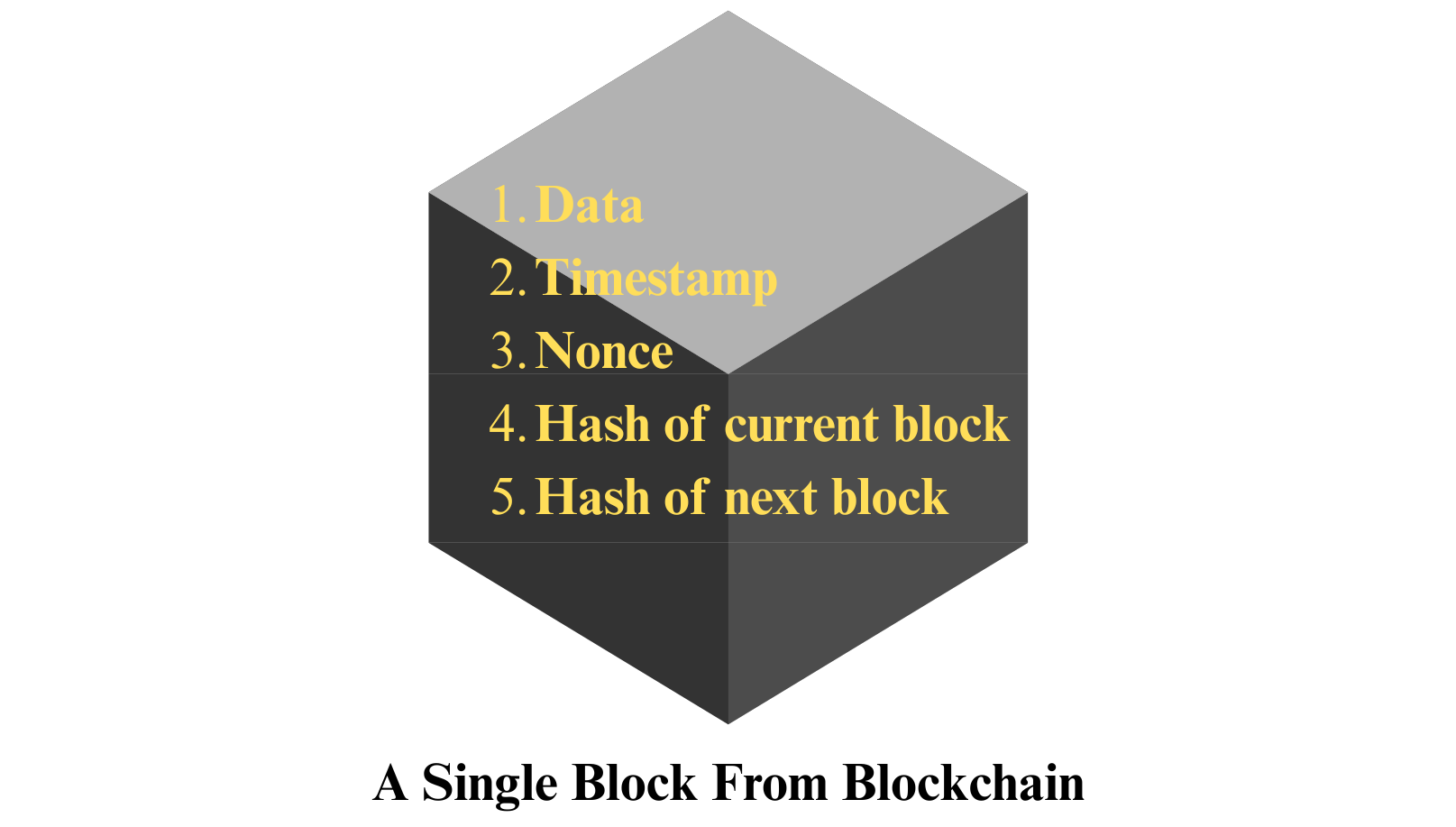
5️⃣ Hash of the Previous Block
Links the block to the previous one, creating the chain.
The Chain Structure
Each block contains the hash of the previous block, making it mathematically linked.
Topic 3: History of Blockchain
Content coming soon...
Topic 4: Mathematical Foundation for Blockchain
Content coming soon...
Topic 5: Cryptography
Content coming soon...
Topic 6: Symmetric & Asymmetric Key Cryptography
Content coming soon...
Topic 7: Elliptic Curve Cryptography (ECC)
Content coming soon...
Topic 8: Cryptographic Hash Functions: SHA256
Content coming soon...
Topic 9: Digital Signature Algorithm (DSA)
Content coming soon...
Topic 10: Merkel Trees
Content coming soon...